Alex Constantine - September 22, 2014
Also see: "Behind the effort to thwart DC's cellphone hackers"
Have you ever stopped to think that your cell phone conversations might be intercepted by so-called “fake” or “interceptor” cell towers? Could domestic surveillance and law enforcement agencies be using such towers to spy on people?
According to a recent investigative piece on newsweek.com, the answer is “yes” — cell towers operated by, or in service of, the government could well be messing with your private communications.
The Internet is abuzz with reports of mysterious devices sprinkled across America—many of them on military bases—that connect to your phone by mimicking cell phone towers and sucking up your data. There is little public information about these devices, but they are the new favorite toy of government agencies of all stripes; everyone from the National Security Agency to local police forces are using them.
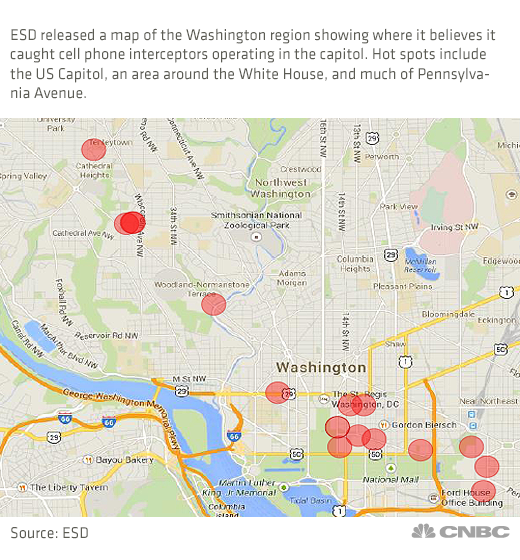
Now the Washington Times reports that suspicious cell towers have been discovered not where they could be used by the government, but could present a real threat to government operations as well as to national security.
According to the Times article, experts have identified interceptor towers near locations where privileged communications are extremely sensitive — the White House and the U.S. Capitol. And who’s secretly doing the listening? Probably foreign agents, says one expert.
“It’s highly unlikely that federal law enforcement would be using mobile interceptors near the Senate,” ESD America CEO Les Goldsmith told the technology website Venture Beat on Thursday.
The towers are also capable of loading spyware onto a mobile device before passing off a victim’s call to a legitimate network.
“My suspicion is that it is a foreign entity,” he told Venture Beat.
The reason Mr. Goldsmith doesn’t suspect U.S. agencies of placing the interceptors is that the federal government already has the capability of tapping directly into the carriers.
After a separate investigation, theblaze.com says that mysterious intercept devices — not necessarily large towers — have been located around the Russian embassy.
“In several locations including on Pennsylvania Avenue in downtown D.C. someone is operating a full-blown intercept where whenever you walk past they actually break open your communications and look at what’s going on on the device,” [Aaron Turner, an expert in mobile security] said.
…it could be anyone “sitting up in an apartment building, it could be a device embedded in a copy machine inside of an office, these cell ‘towers’ don’t have to be big, they don’t have to be sitting on top of a roof. They can be embedded in another piece of equipment or be inside of a wall.”
http://www.westernjournalism.com/fake-cell-towers-possible-interceptors-have-just-been-discovered-in-a-very-scary-place/#m8soOj50i12D3K8D.99