Alex Constantine - August 18, 2014
Greenwald called the report, by NPR reporter Dina Temple-Raston, "a pure and indisputable case of journalistic malpractice and deceit." It's hard to say he doesn't have a point.
The piece is basically a summary of claims made by Recorded Future, described by Temple-Raston as a "big data firm" and "a tech firm based in Cambridge, Mass." She didn't describe it, as she did in a 2012 report (Morning Edition, 10/8/12), as a group with "at least two very important financial backers: the CIA's investment arm, called In-Q-Tel, and Google Ventures. They have reportedly poured millions into the company."
Not only is Recorded Future financially backed by the CIA, the intelligence community is one of its chief clients (along with Wall Street), and In-Q-Tel. It's a registered vendor for the NSA itself, though it refused to tell Greenwald whether it has any actual contracts with the agency.
This is the company that Temple-Raston brought in to substantiate claims by "US government officials" that "revelations from former NSA contract worker Edward Snowden harmed national security"–- without letting listeners know that it was not an independent authority, but an entity with close financial ties to the intelligence community whose claims it was vouching for. This is indeed journalistic malpractice, and merits a correction by NPR.
But what about the substance of the claim that NPR found newsworthy enough to base a segment around? It doesn't pass the laugh test. In essence, Recorded Future is saying that there were significant changes made to encryption software distributed by militant groups after Snowden's revelations–-and that's "good circumstantial evidence" that Snowden was the cause of those changes.
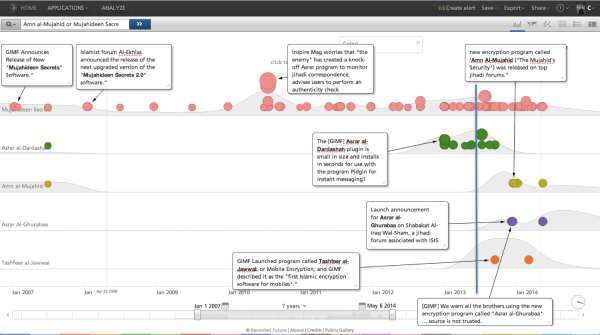
That is, of course, a textbook example of the logical fallacy known as post hoc ergo propter hoc–-Latin for "after this, therefore because of this." But when you actually look at Recorded Future's reports, you see the changes weren't even "after this." The timeline as presented by Recorded Future can be seen above.
The colored dots are activity related encryption programs associated with various groups–-and the blue line is June 2013, when Snowden came out with his revelations. Note that there was a major burst of activity that started well before Snowden came forward and continued afterward–involving Asrar al-Dardashah, a program to encrypt instant messages released in February 2013 by the al-Qaeda-affiliated GIMF. In its timeline, Recorded Future presents this as the first significant change in jihadist transcription techniques since 2007.
But when it comes time to analyze the timeline, this pre-Snowden release mysteriously disappears:
The timeline above tells a compelling story showing how four to five months after the Snowden disclosures both mainstream AQ, as well as the break-off group ISIS, launches three new encryption tools.
Yes, by blatant cherry-picking you can produce "a compelling story"–as in, good enough to fool NPR.
AN/HRJ