Alex Constantine - April 16, 2015
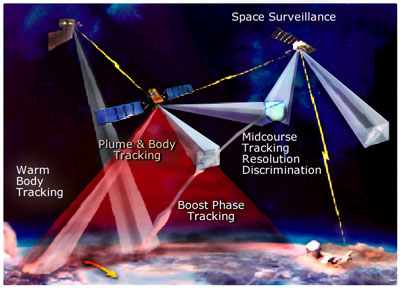
Also see: WikiLeaks publishes huge archive of hacked Sony documents: "Sony Pictures Entertainment CEO Michael Lynton is on the board of trustees of RAND Corporation, an organisation specialising in research and development for the United States military and intelligence sector. The Sony Archives show the flow of contacts and information between these two major US industries, whether it is RAND wanting to invite George Clooney and Kevin Spacey to events, or Lynton offering contact to Valerie Jarrett (a close advisor to Obama) or RAND desiring a partnership with IMAX for digital archiving. With this close tie to the military-industrial complex it is no surprise that Sony reached out to RAND for advice regarding its North Korea film The Interview. RAND provided an analyst specialised in North Korea and suggested Sony reach out to the State Department and the NSA regarding North Korea’s complaints about the upcoming film. The Sony documents also show Sony being in possession of a brochure for an NSA-evaluated online cloud security set-up called INTEGRITY."
----------------
WikiLeaks on Thursday published a searchable database of more than 30,000 documents and 173,000 emails leaked from the Sony Pictures Entertainment breach last year.
WikiLeaks, which publishes leaked, secret and classified information, posted the files in an easily searchable format.
It said they were important to keep in the public eye because of Sony's ties to the White House, its extensive lobbying efforts on behalf of copyright law as well as its "connections to the US military-industrial complex," the group said in a release on its site.
In a statement, Sony said it "vehemently disagrees" with the assertion that the material belongs in the public domain.
"The cyber-attack on Sony Pictures was a malicious criminal act, and we strongly condemn the indexing of stolen employee and other private and privileged information on WikiLeaks. The attackers used the dissemination of stolen information to try to harm SPE and its employees, and now WikiLeaks regrettably is assisting them in that effort," the statement read.
The Culver City, Calif.-based company's website was crippled beginningThanksgiving day of 2014 by hackers who also stole files and emails.
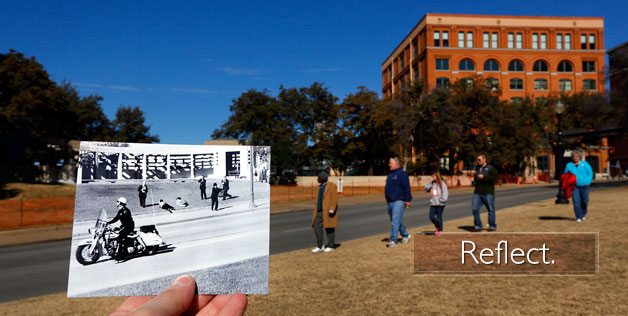
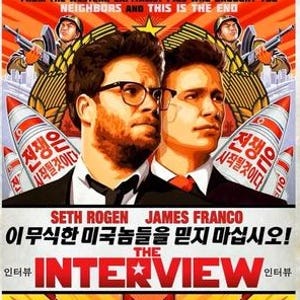
The attack was later linked to North Korea in revenge for Sony's planned release of the Seth Rogen and James Franco movie, The Interview, which made fun of the secretive nation and ended with the assassination of its leader, Kim Jong Un.
The documents and emails give an easily-accessible picture of what's normally hidden at a large multinational corporation.
They include connections between Sony and the Democratic Party, an email asking executives to donate to a $50,000 for New York Gov. Andrew Cuomo for his anti-piracy work and links to the RAND Corporation, which WikiLeaks calls a part of "the military-industrial complex."
There's also a great deal of information about the movie world, including emails about Sony's films as well as movies and TV shows produced by rivals.
Assange himself is under house arrest inside Ecuador's embassy in London for the past two years. He has been accused of rape in Sweden, where prosecutors have been seeking is extradition.
The legal issues surrounding the postings are somewhat cloudy, said Kevin Smith, who directs the Office of Copyright and Scholarly Communication at Duke University in Durham, N.C.
The original files and emails would have been copyrighted by whoever created them, as "copyright is automatic, it literally follows the pen," he said.
Posting the files without permission would be infringement upon that copyright.
Stolen, the word Sony uses, would mean the files and emails were taken and no longer accessible to the entity that originally owned them. That's usually not the case with online material because the original files or emails remain intact, they've simply been copied.
However in the original hack attack on Sony, many of the company's computer servers were damaged, meaning the original files actually were destroyed.
But what that means for WikiLeaks as the secondary publisher of them after the hackers first posted them is unclear.
"We just don't have a word for this," said Smith.
 "This archive shows the inner workings of an influential multinational corporation. It is newsworthy and at the centre of a geo-political conflict. It belongs in the public domain. WikiLeaks will ensure it stays there," said Julian Assange, WikiLeaks' founder.
"This archive shows the inner workings of an influential multinational corporation. It is newsworthy and at the centre of a geo-political conflict. It belongs in the public domain. WikiLeaks will ensure it stays there," said Julian Assange, WikiLeaks' founder.